Just testing the Virtual Machine Contributor role and if you have public IP and Network Security Group selected (things that you would assume would be wanted when creating a VM) you get a Validation failure
{"code":"InvalidTemplateDeployment","message":"Deployment failed with multiple errors: 'Authorization failed for template resource 'toggen-vm-03-nsg' of type 'Microsoft.Network/networkSecurityGroups'. The client '[email protected]' with object id '255b1f77-a36c-466a-9a88-6546ffb25529' does not have permission to perform action 'Microsoft.Network/networkSecurityGroups/write' at scope '/subscriptions/<SUBSCRIPTION ID>/resourceGroups/Toggen-VM/providers/Microsoft.Network/networkSecurityGroups/toggen-vm-03-nsg'.:Authorization failed for template resource 'toggen-vm-03-ip' of type 'Microsoft.Network/publicIpAddresses'. The client '[email protected]' with object id '255b1f77-a36c-466a-9a88-6546ffb25529' does not have permission to perform action 'Microsoft.Network/publicIpAddresses/write' at scope '/subscriptions/<SUBSCRIPTION ID>/resourceGroups/Toggen-VM/providers/Microsoft.Network/publicIpAddresses/toggen-vm-03-ip'.'"}
So it looks like you need to add permissions or a custom role of:
Microsoft.Network/networkSecurityGroups/write
Microsoft.Network/publicIpAddresses/write
Get-AzRoleDefinition -Name "Virtual Machine Contributor" | ConvertTo-Json | Out-File "VirtualMachineContributor.json"
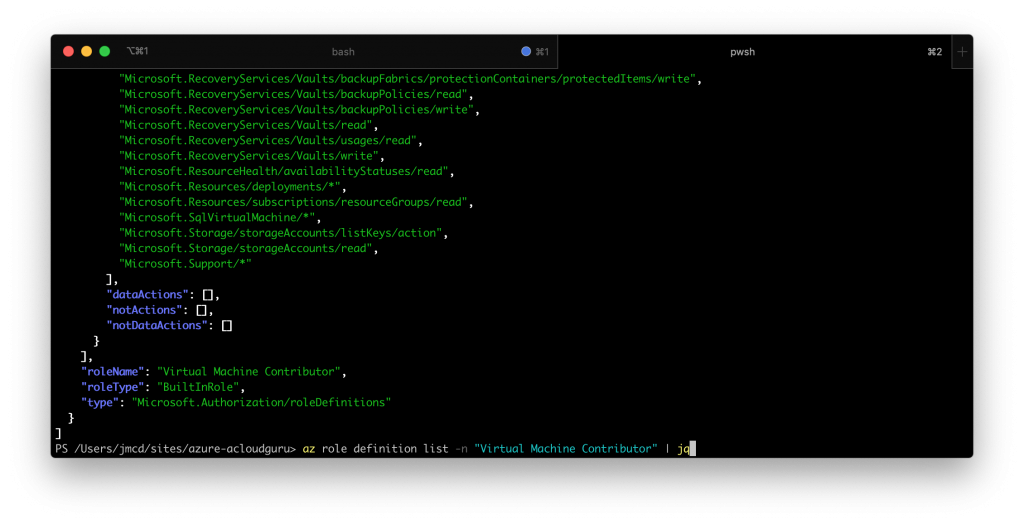
Above we get a default defintion of the Virtual Machine Contributor from Azure using power shell or using az-cli
az role definition list -n "Virtual Machine Contributor"
Add the read and write options for NSG and Public IP’s, remove the “Id” property, change “IsCustom” to true and change assignable scope from / to your subscription Id.
Then load it to Azure
New-AzRoleDefinition -InputFile ./VirtualMachineContributorCustom.json
{
"Name": "Toggen Virtual Machine Contributor",
"IsCustom": true,
"Description": "Lets you manage virtual machines, Including adding PublicIP and NetworkSecurityGroups but not access to them, and not the virtual network or storage account they're connected to.",
"Actions": [
"Microsoft.Network/networkSecurityGroups/read",
"Microsoft.Network/networkSecurityGroups/write",
"Microsoft.Network/publicIpAddresses/write",
"Microsoft.Network/publicIpAddresses/read",
"Microsoft.Authorization/*/read",
"Microsoft.Compute/availabilitySets/*",
"Microsoft.Compute/locations/*",
"Microsoft.Compute/virtualMachines/*",
"Microsoft.Compute/virtualMachineScaleSets/*",
"Microsoft.DevTestLab/schedules/*",
"Microsoft.Insights/alertRules/*",
"Microsoft.Network/applicationGateways/backendAddressPools/join/action",
"Microsoft.Network/loadBalancers/backendAddressPools/join/action",
"Microsoft.Network/loadBalancers/inboundNatPools/join/action",
"Microsoft.Network/loadBalancers/inboundNatRules/join/action",
"Microsoft.Network/loadBalancers/probes/join/action",
"Microsoft.Network/loadBalancers/read",
"Microsoft.Network/locations/*",
"Microsoft.Network/networkInterfaces/*",
"Microsoft.Network/networkSecurityGroups/join/action",
"Microsoft.Network/networkSecurityGroups/read",
"Microsoft.Network/publicIPAddresses/join/action",
"Microsoft.Network/publicIPAddresses/read",
"Microsoft.Network/virtualNetworks/read",
"Microsoft.Network/virtualNetworks/subnets/join/action",
"Microsoft.RecoveryServices/locations/*",
"Microsoft.RecoveryServices/Vaults/backupFabrics/backupProtectionIntent/write",
"Microsoft.RecoveryServices/Vaults/backupFabrics/protectionContainers/protectedItems/*/read",
"Microsoft.RecoveryServices/Vaults/backupFabrics/protectionContainers/protectedItems/read",
"Microsoft.RecoveryServices/Vaults/backupFabrics/protectionContainers/protectedItems/write",
"Microsoft.RecoveryServices/Vaults/backupPolicies/read",
"Microsoft.RecoveryServices/Vaults/backupPolicies/write",
"Microsoft.RecoveryServices/Vaults/read",
"Microsoft.RecoveryServices/Vaults/usages/read",
"Microsoft.RecoveryServices/Vaults/write",
"Microsoft.ResourceHealth/availabilityStatuses/read",
"Microsoft.Resources/deployments/*",
"Microsoft.Resources/subscriptions/resourceGroups/read",
"Microsoft.SqlVirtualMachine/*",
"Microsoft.Storage/storageAccounts/listKeys/action",
"Microsoft.Storage/storageAccounts/read",
"Microsoft.Support/*"
],
"NotActions": [],
"DataActions": [],
"NotDataActions": [],
"AssignableScopes": [
"/subscriptions/716afb31-54e7-4e43-8c36-e29336b31ec3"
]
}
0 Comments