I am using a Windows 10 PC on my LAN that I am trying to send a WOL magic packet using WakeMeOnLan.exe . I wanted to check with Wireshark whether the packets were being sent but using a capture filter or wol on the correct interface returned nothing
The problem
WakeMeOnLan sends non-standard WOL packets. Normally a WOL packet should be UDP port 9 but the WakeMeOnLAN packets are shown in the capture as
Protocol : "? KNXnet/IP"
Info: "? Unknown Service Family."
WakeMeOnLAN is sending a UDP packet to port 40000
Working Capture Filters with WakeMeOnLAN defaults
Capture broadcasts to ethernet
eth.addr == ff:ff:ff:ff:ff:ff
Capture packets sent to the specific device using its MAC Address
eth.addr == 00:11:33:43:96:9F
To get Wireshark to see WOL Protocol change to port 9
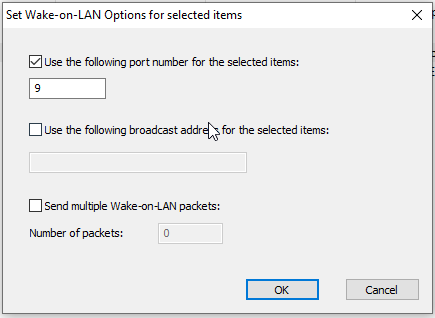
In the WakeMeOnLAN gui, right click on a device and choose "Change wake up settings for the selected items" enter port 9
Wireshark then displays the packet as WOL

WakeMeOnLAN Command line
# wakemeonlan.exe /wakeup <ETHERNET_MAC_ADDRESS>
wakemeonlan.exe /wakeup 00:11:33:42:9B:9E

0 Comments