I recently tried to connect a Synology OpenVPN Server with both Tunnelblick 3.8.8beta02 and OpenVPN Connect 3.3.2 and they both would not connect, a problem many are having, as discussed over at the OpenVPN forums https://forums.openvpn.net/viewtopic.php?f=37&t=32568
This is my fix which allows connection from OpenVPN Connect and Tunnelblick
How to connect OpenVPN Connect and Tunnelblick to Synology NAS
Download EasyRSA https://github.com/OpenVPN/easy-rsa/releases
I used the EasyRSA-3.0.8-win64 package on Windows 10. Unpack it to somewhere that doesn't have spaces in the path or it will choke.
Create a Certificate for the Synology using EasyRSA
Here are the commands to get EasyRSA setup.
When you build the CA (build-ca) you will be prompted for a passphrase for the Certificate Authority cert.
When building the OpenVPN server cert (build-server-full) you should add the command option nopass so that the Synology VPN server can load the certificate without being prompted for a passphrase
cd C:\Temp\EasyRSA-3.0.8
EasyRSA-Start.bat
./easyrsa init-pki
./easyrsa build-ca
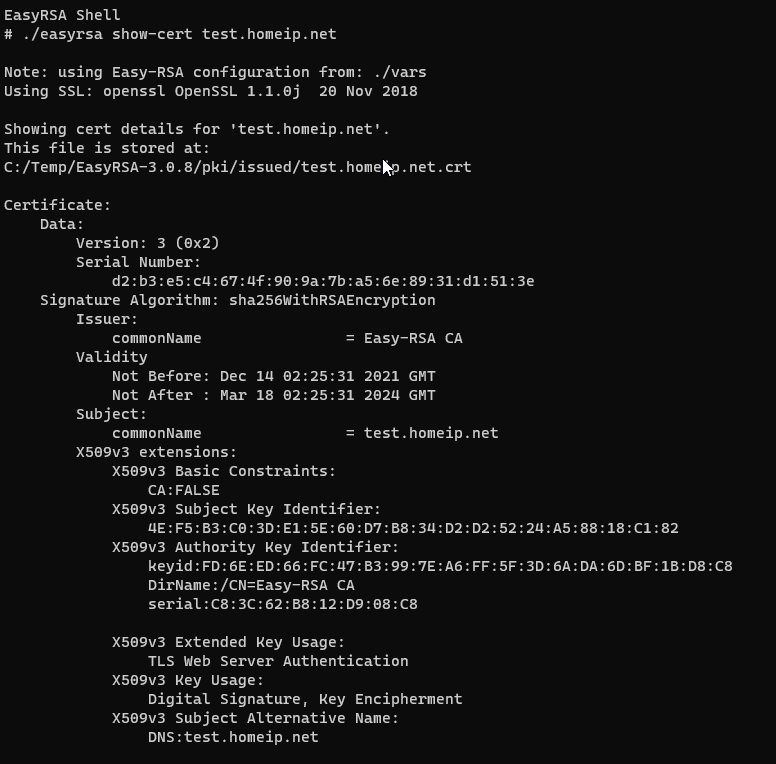
./easyrsa build-server-full testhost.homeip.net nopass
Although a fully qualified resolveable hostname such as testhost.homeip.net is nice it can be whatever you want (e.g. server1, ovpnserver, hostname.domainname etc).
Upload the Certificate to the Synology NAS
I'm using DSM 7.0.1-42218
- Open Control Panel => Security => Certificate => Add (click button)
- Choose "Add a new certificate" and click Next
- Enter a Description i.e. "EasyRSA Cert" and select "Import Certificate" and click next
- For Private Key, Certificate and Intermediate Certificate select the files you just generated from the following paths
- C:\Temp\EasyRSA-3.0.8\pki\private\testhost.homeip.net.key
- C:\Temp\EasyRSA-3.0.8\pki\issued\testhost.homeip.net.crt
- C:\Temp\EasyRSA-3.0.8\pki\ca.crt
- Click OK to add the cert
- Above the list of Certicates (by default there will only be a "synology" cert in the list) click the "Settings" button
- On the configure tab find the VPN Server entry and then select the certificate name as above (testhost.homeip.net) and acknowledge you want to save the change.
- The VPN Server should reload and you can now go to VPN Server (on the Main Menu) and select OpenVPN under "Setup VPN Server" and click the Export Configuration button
- This will trigger the download of an openvpn.zip file, unpack it and then edit the VPNConfig.ovpn file "remote" option to match the remote OpenVPN server address
# replace this
# remote YOUR_SERVER_IP 1194
# with whatever hostname or IP resolves to your OpenVPN server
remote testhost.homeip.net 1194
Once you have finised editing import VPNConfig.ovpn into OpenVPN Connect 3.3.2 and connect!
The OpenVPN Connect client does show a warning about a Missing external certificate, but you can just kick continue no harm no foul.
An example of a certificate generated as above note the extended key usages.

0 Comments