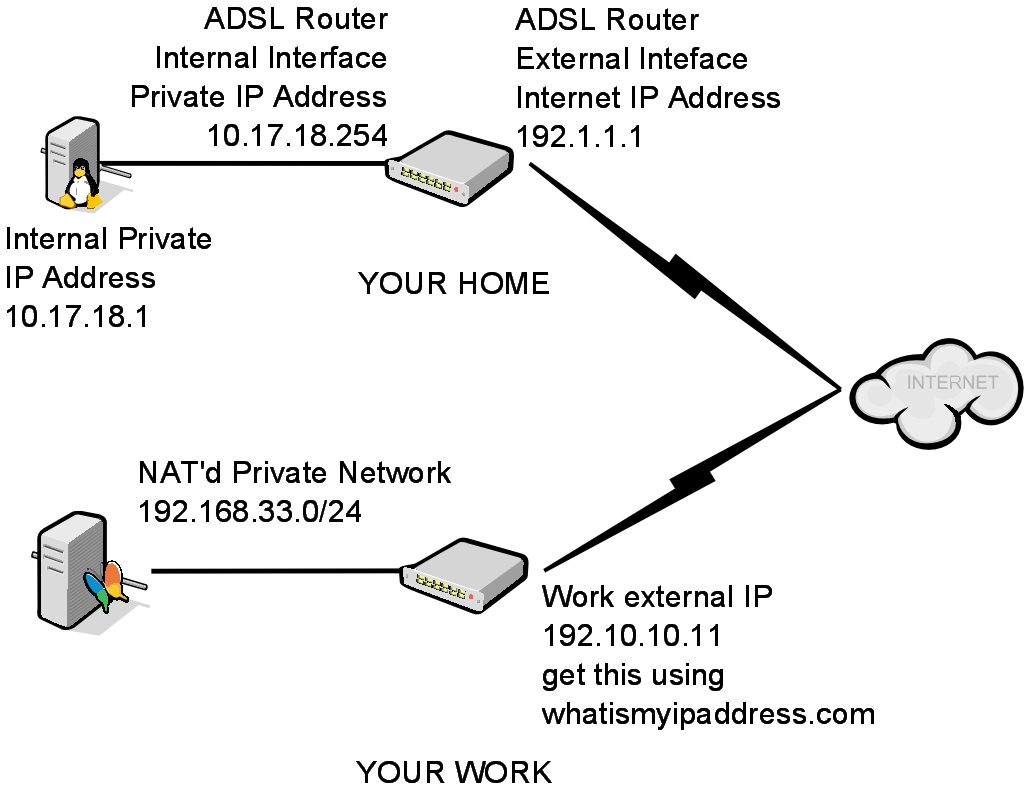
An example Home/Work setup:
If you enable ufw remotely without specifying a correct ssh rule you may lock yourself out of your remote Ubuntu box.
Before you can setup an ssh allow rule you need the following configuration and information:
- Port forwarding TCP port 22 from the external Interface of your home router to your internal Ubuntu Computer (Port 22 traffic arriving at 192.1.1.1 forwards to 10.17.18.1)
- The Private IP Address of your HOME Ubuntu based computer (10.17.18.1)
- The External Internet facing IP address of your WORK internet router (192.10.10.11) - Use whatismyipaddress.com from your work workstation to figure this out
- Obviously your work network administrator needs to allow outgoing port 22 traffic to your home external ip address (you may not be able to get this done so a work-a-round is to move your Ubuntu ssh server to listen on port 443 and modify your home port forwarding to suit. Many corporate networks don't block port 443 due to it's use with https:// )
So in plain english you want to allow TCP traffic from the external interface of your work network (192.10.10.11) to the IP address of your internal Ubuntu box (10.17.18.1) on port 22.
Here are the commands:
# after logging in remotely from your work to your home Ubuntu Box
# first add the correct rule to allow the Work to home connection
root@myhomebox:~# ufw allow proto tcp from 192.10.10.11 to 10.17.18.1 port 22
# once you have added the rule it is safe to enable the ufw firewall
root@myhomebox:~# ufw enable
# say yes
Command may disrupt existing ssh connections. Proceed with operation (y|n)? y Firewall is active and enabled on system startup
# if you have done the above rule correctly your ssh connection will still be up
# you can then check the status and list the rule as follows
root@myhomebox:~# ufw status
Status: active
To Action From -- ------ ----
10.17.18.1 22/tcp ALLOW 192.10.10.11
# if you want to see the underlying iptables configuration issue:
iptables -L -n

0 Comments
Trackbacks/Pingbacks